More home and office WiFi routers and network attached storage (NAS) devices have been targeted by malware dubbed VPNFilter than first reported, says Cisco Systems’ Talos threat intelligence service.
First reported two weeks ago, the malware had been found in at least 500,000 devices from five manufacturers in at least 54 countries. But on Wednesday Cisco said it has now seen infections in some devices made by Asus, D-Link, Huawei, Ubiquiti, UPVEL, and ZTE. New infected devices were also discovered in the first group of manufacturers, which include Linksys, MikroTik, Netgear, and TP-Link.
The link to the Cisco blog above has a full list of makes and models that have been infected. Owners should note that some devices — like the Cisco Linksys E1200 and E2500 are several years old (these were made by Cisco before it sold Linksys to Belkin in 2013) many the models that can be infected are new.
The list may be incomplete, Cisco added.
Researchers have also discovered a new stage 3 module that injects malicious content into web traffic as it passes through an infected network device. This module allows whoever is behind the malware to deliver exploits to endpoints via a man-in-the-middle capability, injecting malicious code into without the user’s knowledge.
“With this new finding, we can confirm that the threat goes beyond what the actor could do on the network device itself, and extends the threat into the networks that a compromised network device supports,” said Cisco.
And if that’s not enough researchers discovered an additional stage 3 module that provides any stage 2 module that lacks a kill command the capability to disable the device. When executed, this module removes traces of the VPNFilter from the device, and then renders the unit unusable.
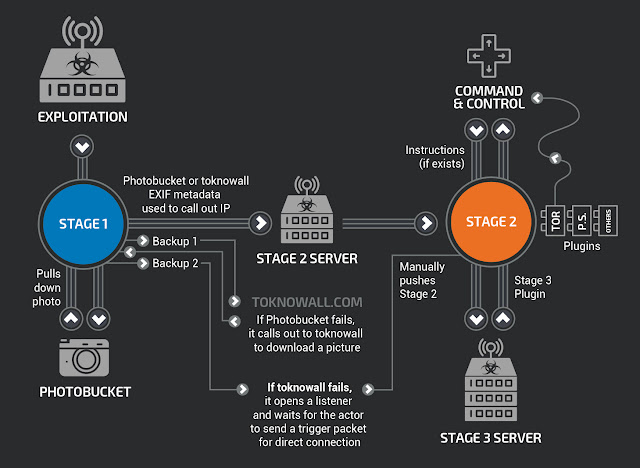
(Cisco diagram of the original two-stage malware it found)
What can you do? First, check the Cisco blog to see if your unit is on the list. If you have any of the devices known or suspected to be affected, make sure it has the manufacturer’s latest security patches. You may also have to reset the device to the factory default and reboot to remove the malware (see below). Internet service providers that provide SOHO routers to their users reboot the routers on their customers’ behalf.
Even if your device isn’t on the list users of SOHO routers and/or NAS devices may want to reset and reboot them. To find out how to do it safely see this blog from the SANS Institute. Or, if the device is several years old, think about buying a new one.
“These new discoveries have shown us that the threat from VPNFilter continues to grow,” said Cisco [Nasdaq: CSCO]. “In addition to the broader threat surface found with additional targeted devices and vendors, the discovery of the malware’s capability to support the exploitation of endpoint devices expands the scope of this threat beyond the devices themselves, and into the networks those devices support. If successful, the actor would be able to deploy any desired additional capability into the environment to support their goals, including rootkits, exfiltration capability and destructive malware.”
