Exploits of holes in Microsoft Office have been around for years, but Cisco Systems’ Talos threat intelligence service has sighted a new email-based campaign that combines two exploits in hopes of doubling their effect.
Fortunately, the company notes in a blog, the creators made some errors so the effect of the attempt has been blunted. But the discovery serves as another warning that threat actors are creative, and of the necessity to speed patching procedures.
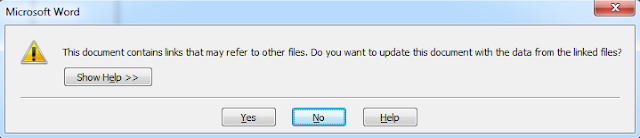
“Attackers are obviously trying to find a way around known warning mechanisms alerting users about potential security issues with opened documents,” Cisco notes. The idea, apparently is to avoid prompts Office should give if administrators have configured the suite to not automatically execute macros or run remote files. Instead Office gives a warning and asks users permission to run the file.
However, possibly because there was poor testing or quality control this version of the malware isn’t working.
The package combines CVE-2017-0199, disclosed in April, which allows attackers to include Ole2Link objects within RTF documents to launch remote code when HTML application files are opened and parsed by Microsoft Word, with an five-year old exploit, CVE-2012-0158, It allow remote attackers to execute arbitrary code. Both have already been patched.
The particular attack seen by Cisco started with an email with a supposed purchase order attachment. That document is an RTF file including an Ole2Link to a remote document. Tested on a vulnerable version of Office, Word started to convert the downloaded document but then crashed when CVE-2012-0158 started to run. Perhaps, Cisco speculates, the authors didn’t realize what might happen if these two vulnerabilities tried to run together, which is a memory protection error.
“If the attackers would have been just a little bit more technically savvy they would realize this problem and easily fix it to make these two exploits work together successfully without the prompt to load the remote content being displayed to the end-user,” says Cisco — although it notes that the shellcode in the document containing the CVE-2012-0158 exploit will be successfully executed if there are no other open RTF files on the infected system.
This kind of attack won’t work on a system that has received a patch for either vulnerability. Cisco suspects the threat actors hoped the combination would avoid Word displaying the warning prompt. Another possibility was to avoid behavioral detection systems which may be triggering on the combination of Ole2Link in a Word document and a download of an HTA file.
Either way, the lesson to infosec pros is that patching is as vital as ever. The blog notes that the three-month old CVE=2017-0199 has now become one of the most commonly used vulnerabilities exploited in email attacks. That means in large enterprises there’s no longer the luxury of taking time to test a patch against all combinations of hardware and software before deploying. Patching testing procedures must be more efficient.
