
20 years ago, security was relatively simple: do a virus-scan on your floppy disk before you insert it. Today, with everything from embedded systems to IP phones connected to one another, it’s more complicated. Here are six security problems that should be on every CIO’s radar screen.
By Greg Meckbach,
Editor, Network World Canada
Malicious Portable Document Format files
Adobe Systems Inc. has been a favourite target of hackers due to the popularity of its free Portable Document Format (PDF) reader. The latest vulnerability allows hackers to exploit a dynamic link library in Microsoft Corp.’s Windows and the current version of Adobe Acrobat. In September, Microsoft published a work-around with Enhanced Migration Experience Toolkit but users still need to handle PDF files, especially those received from unknown third parties, with caution.

Voice, video and data convergence
As more companies combine voice, video and data on to the same network, the phone and video systems can be just as vulnerable as the IT system. At a recent Forrester Research Inc. conference, an expert from Sipera Systems Inc. showed how insiders can use freeware to eavesdrop and record video conferences and voice over IP phone calls. Speakers also talked about ways to deter and prevent such attacks.

Embedded systems
This problem is a concern for industrial users. Last summer, Belarussian vendor VirusBlockAda discovered miscreants were trying to hack into embedded systems using supervisory control and data acquisition, or SCADA systems, made by Siemens AG. The creators of the malware, dubbed Stuxnet, also reportedly stole encryption keys made by semiconductor manufacturers Realtek Semiconductor Corp. and JMicron Technology Corp. A German security expert suggests Stuxnet’s real target was an Iranian nuclear facility.
Malicious executable downloads
The problem of employees downloading executable files from spam and other sources, not realizing they could be malicious, is not a new problem. But it continues to be a major problem and Hewlett Packard Development Co. LP recently published a report from its newly-acquired TippingPoint unit predicting that in the future, companies will, by default, prohibit most employees from downloading files unless they have express permission to do so.

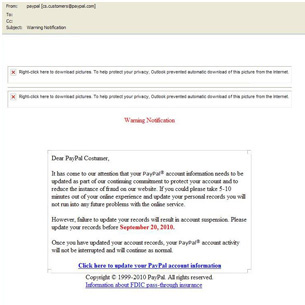
Asking employees outright for sensitive data
At last summer’s Defcon security conference, organizers held a contest designed to test the security of major firms. Contestants were encouraged to attack using so-called social engineering, meaning they called the companies, pretended to be on official business and asked for information that could potentially help a hacker, such as the operating systems, anti-virus software and browser the firms were using. Of the 135 people who were called, only five refused to answer questions.
Virtualization
Locking down servers is not as easy when applications move among servers using virtual machines. There are ways of making virtualization secure, but at the recent VMWorld conference, an engineer with BeyondTrust Software Inc. claimed hackers can manipulate the service console of VMware Inc.’s ESX virtualization product. This means they could steal virtual machine disk files and erase log files.