The vulnerability of BlackBerry’s PIN-to-PIN messaging service is not a deadly new flaw, as news reports Wednesday of the discovery of cyber-security memo issued to federal departments earlier this year about it would suggest.
BlackBerry devices are issued a unique eight-digit PIN independent of the users account or email address. If a BlackBerry user shares this PIN with other BlackBerry device users they can exchange messages even in the event of a BlackBerry network outage or power outage that disrupts email and text messaging.
The scare — according to the British-based online news service The Register — began yesterday when news leaked out that Public Safety Canada, the agency that oversees national security, issued a memo warning federal employees who communicate using PIN-to-PIN. The memo said the service is not “suitable for exchanging sensitive messages,” because information exchanged through the service could be inadvertently read by other BlackBerry users.
RELATED CONTENT
Update on Canadian wireless public safety network
Report: Canada’s cyber-security falling short
“Although the PIN-to-PIN messages are encrypted the key used is a global cryptographic key that is common to every BlackBerry device all over the world,” the memo said. “Any BlackBerry device can potentially decrypt all PIN-to-PIN messages sent by any other BlackBerry device.”
It now appears that memo could be an update or rehash of the one sent by CSEC over two years ago.
Here’s an excerpt of that March 2011 memo:
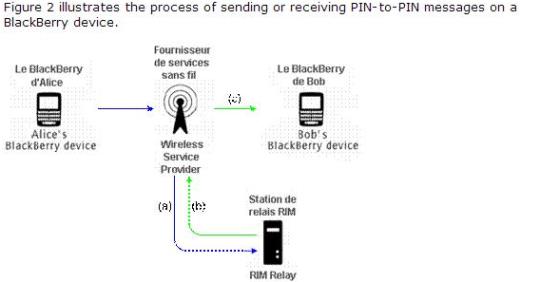
The CSEC, however, said PIN-to-PIN messaging is typically faster than normal email because it passes through fewer servers so it would be useful in emergency communication situations where departmental email servers are down but wireless service providers and BlackBerry relay are still available.