Companies and individuals rely on the SSL (secure socket layer) encryption to secure passwords, credit card information and other personal and sensitive information. However, many organizations have no way of protecting their data once its SSL private keys are compromised, according to Internet security research firm Netcraft Ltd.
The company said that recent disclosure of the United States National Security Agency’s mass surveillance of Internet traffic have shown that harvesting encrypted traffic for possible decryption later on is possible. It’s actually a practice used by cyber espionage and crime networks based in other countries as well such as Saudi Arabia and China, according to Netcraft.
“The reason that governments might consider going to great lengths to log and store high volumes of encrypted traffic is that if the SSL private key to the encrypted traffic later becomes available – perhaps through court order, social engineering, successful attack against the Web site or through crypto analysis – all of the site’s hystorical traffic may then be decrypted at once,” a post on the Netcraft site said.
SSL pertains to cryptographic protocols that provide communication security over the Internet by encrypting segments of network communications. SSL works through a combination of encryption and decryption routines existing between the hosting computer and browser such as Internet Explorer, Chrome, Firefox or Safari to secure communications.
“When PFS is used, the compromise of an SSL site’s private key does not necessarily reveal the secrets of past communication,” Netcraft said. “Connections to SSL sites which use PFS have a per-session key which is not revealed if the long-term private key is compromised.”
Even though PFS was invented in 1992, pre-dating SSL by two year, it is not used in a majority of sites.
“The use of PFS is dependent on the negotiation between the browser and the Web site successfully agreeing on a PFS cipher suite,” according to Netcraft.
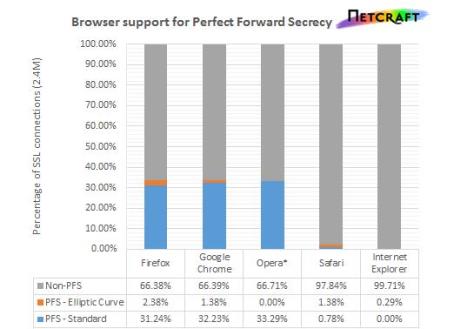
In a test last month of cipher suites of Internet explorer, Google Chrome, Firefox, Safari and Opera against 2.4 million SSL site, Netcraft found that support for PFS varied significantly among the browsers.
“Only a tiny fraction of Internet explorer’s SSL connections operated with PFS, whereas Google Chrome, Opera and Firefox were protected for approximately one third of connections,” according to Netcraft. “Safari fared only a little better than Internet Explorer.”
How does this relate to government-sponsored mass Web surveillance?
Netcraft reports that many of the companies affected by the NSA’s Prism program do not use PFS cipher suites when visited in any of the major browsers.
But before conspiracy theorists speculate on why PFS is not more widely used, Netcraft was quick to add that “performance concerns” are likely behind some browsers’ reluctance to support it. Use of PFS can result in some performance penalty for browsers.
“The lack of clear in-browser notifications of the use of PFS cipher suites may persuade popular SSL sites to forgo the protection PFS offers, which typical users do not notice, to instead improve the web site’s performance, which typical users do notice,” said Netcraft.