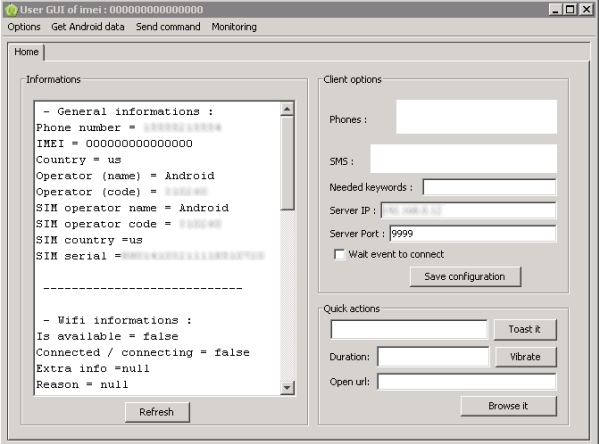
According to Symantec blogger Andrea Lelli, the AndroRAT APK binder allows an attacker to easily infect any legitimate Android app (APK is the standard application format for Android apps). When the user installs the Trojanized app, he also installs the RAT.
Symantec has identified 23 instances of popular Android apps repackaged with the AndroRAT remote access tool.
Symantec says the creators of a Java RAT that supports multiple operating systems, Adwind, appear to be incorporating an Android module based on AndroRAT’s open source code.
Symantec says it has detected only a few hundred infections worldwide, primarily in the U.S> and Turkey, but infection numbers are rising.
“While AndroRAT is not showing a particularly high level of sophistication just yet, with the open source nature of its code and with its popularity growing, it has potential to evolve and grow into a more serious threat,” writes Lelli.