Security threats to watch for in 2015
The big data bonanza, high-tech wearables for our wrists, the Internet of things and sensors that could let our toasters talk to our fridges. A lot of technology developments have been going down the pipeline the past 12 months that promise to make life and work easier and fun in the coming year.
However, with these new developments also come new security threats, warns a recent report from security vendor Websense.
Large-scale data breaches at retail chains and government agencies as well as attacks on data stored in the cloud made the headlines in 2014, expect to see more of the same in the coming year. However, the 2015 Security Predictions from Websense also outlines some of the emerging trends that IT teams and security administrators need to keep a close eye on in the coming year.
“When we you look back at 2014 and take note of the attacks that transpired, you might wonder ‘how can 2015 be any worse?’,” said Carl Leonard, principal security analyst at Websense. “In fact in some instance attack trends we saw in 2014 were just proof-of-concepts – in 2015, we’ll see better targeted and more complex attacks.”
Here are nine areas that security practitioners need to pay close attention to in 2015.
Image from Shutterstock.com

1. Healthcare records at risk
Whe it comes to richness of data, it can be argued that nothing comes close to medical records and patient data. “No other tipe of record contains as much Personal Identifiable Information (PII) that can be used in a multitude of different follow-up attacks and various types of fraud,” according to Websense.
Healthreacords contain vital information on identity (name, address, social security) and are often linked to financial and insurance information.
With millions of patient records now in digital form “healthcare’s biggest security challenege in 2015 will be keeping personally identifiable information from falling through the security cracks and into the hands of hackers,” said Leonard.
Image from Shutterstock.com

At the heart of the Internet of Things are the sensors that help machines detect one another, communicate to each other and connect to the Internet. Sensors will be near and dear to the heart of hackers.
While it is entirely possible for hackers to hack into your thermostat or connected car, criminal elements have their eyes set on the enterprise applications of IoT rather than in the consumer space.
Websense predicts that in 2015, there will be at least one major breachor an organization via Internet-connected devices. “The Internet of Things is set to explde and be one of the main sources of headaches for CSO in the comming year, inheriting the title from the bring-your-own-device intitiatives in the past.”
Image from Shutterstock.com

Some changes are in the card for credit card attacks as retail operations step up security with the use of measures like Chip and PIN technology, according to Websense.
The value of stolen information from credit cards rapidly decrease as financial institutions flagged the theft and cancel the cards. To squeeze more value out of their criminal activities, attackers will begin modifying their malware to steal more information from the cards to inlcude credentials and data associated with the terminal, loyalty programs and other store-related information.
“If they can collate their massive data and collection efforts, they can vegin to assemble the individual pieces of data and collect whole profiles of individual users, consisting of multiple credit cards, regional and geographic data,personal information and behaviour,” the report said. “This persona, pulled from the criminal cloud, will then be worth considerably more than the simple credit card number they have stolen.”

The old news is that mobile devices will be increasingly targeted next year. The new news is, mobile attacks will be perpetrated for broader credential-stealing and authentication attacks at a later date.
As more and more organizations use smart phones and tablets to access the cloud where they store sensitive information, criminals will increasingly go after mobile devices not just to crack a phone code or steal data from the device, but also to use the device as a way to gain entrance to the corporate cloud.
Authentication will be an even hotter security issue in 2015 as new deployments of out-of-band mobile and social authentication develop. Expect attacks on social credentials and out-of-band devices to grow massively. Watch out for malicious code that intercept text or code generation authentication elements built into mobile programs.

Remember Heartbleed and Shellshock?
In 2015, at least one major data breach will trace its orginins to cinfidential company data improperly transmitted or secured on publicly available cloud storage sites based on old code foundations.
Since nobody builds from scratch, the speed with which developers use third party tools is astounding. Unfortunately, security is still not built-into most development cycles.
“Old source code is the new Trojan horse waiting to be exploited and open source code is only the beginning,” according to Leonard. “With so much code written and in use, it’s impossible to catch every dormant exposure point until they’ve been executed.”
Image from Shutterstock.com

In recent years, email has taken the backseat to the Web as a preferred attack vector, expect that to change in 2015. Polymorphic Domain Generating Algorithms and ever changing evasion techniques will “test the limits of most cuurent security solutions,” according to Websense.
There’s a growing trend towards the use of emails that do not contain a link or spam message. Because the sender and text are randomized and the body of the email host has no malware or links that can be analyzed, the email is able to bypass most security solutions. These emails as used as a reconnisanace step for another attack.
By automating the attack process across an organization, “attackers can use this method to validate credentials and prepare more effectively for other penetrating aspects of an attack,” according to Websense.

As the use of cloud-based and social tools continue to grow in the enterprise, cyber crininals will increasingly use legitimate hosted sites to launch their command and control malware.
Network administrators typically flag traffic moving through suspicious sites but rarely check traffic going to Google docs or Twitter.
Image from Shutterstock.com
In 2013, the Syrian Electronic Army (SEA) hijacked the associated Press Twitter account and falsely claimed the White House had been bombed and President Obama was injured. Back then this type of attack was exceptional, in 2015 it will likely become the norm.
Websense foresees other radical organizations adotping the methods used by SEA. This can enable such groups to cause “immediate and severe market, economic, social and political damage.”
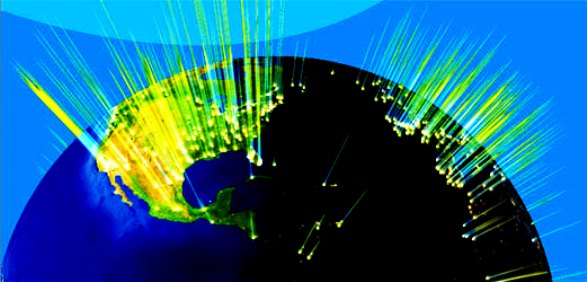
For several years now, there have been numerous accounts of nation-states actively engaging in cyber war planning and attacks. Websense foresees “new recruits to the global cyber war table” in 2015.
The security company has not named any specific groups or possible orginating location but said “we will see an increase in looosely affiliated cells that conduct cyber-terrorist or cyber warfare initiatives independent from, but in support of, nation-state causes.”
The security firm said enterprise and government authorities should watch for increasing cyber espionage activities from “countries with hig forecasted global economic growth.”
“These countries are more likely to be the next to engage in cyber war and espionage activities to protect and advance their growing influence,” Websense said
Image from Shutterstock.com